The following table represents the types of static filters and their selection criteria:
Filter types and criteria
| Static filter type | Selection criteria |
|---|---|
| Source-port | Inbound traffic from a designated, physical source-port will be forwarded or dropped on a per-port (destination) basis. |
| Multicast | Inbound traffic having a specified multicast MAC address will be forwarded to outbound ports (the default) or dropped on a per-port (destination) basis. |
| Protocol | Inbound traffic having the selected frame (protocol) type will be forwarded or dropped on a per-port (destination) basis. |
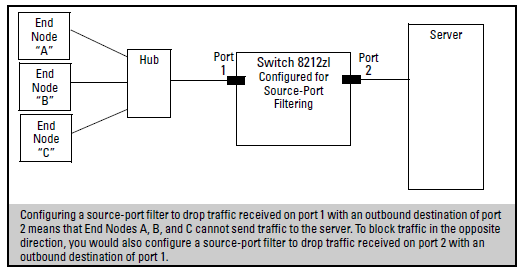
This filter type enables the switch to forward or drop traffic from all end nodes on the indicated source-port to specific destination ports.
-
You can configure one source-port filter for each physical port and port trunk on the switch. (See Defining and configuring named source-port filters.)
-
You can include all destination ports and trunks in the switch on a single source-port filter.
-
Each source-port filter includes:
When you create a source-port filter, the switch automatically sets the filter to forward traffic from the designated source to all destinations for which you do not specifically configure a “drop” action. Thus, it is not necessary to configure a source-port filter for traffic you want the switch to forward unless the filter was previously configured to drop the desired traffic.
-
When you create a source port filter, all ports and port trunks (if any) on the switch appear as destinations on the list for that filter, even if routing is disabled and separate VLANs and/or subnets exist. Where traffic would normally be allowed between ports and/or trunks, the switch automatically forwards traffic to the outbound ports and/or trunks you do not specifically configure to drop traffic. (Destination ports that comprise a trunk are listed collectively by the trunk name—such as Trk1— instead of by individual port name.)
-
Packets allowed for forwarding by a source-port filter are subject to the same operation as inbound packets on a port that is not configured for source-port filtering.
-
With multiple IP addresses configured on a VLAN, and routing enabled on the switch, a single port or trunk can be both the source and destination of packets moving between subnets in that same VLAN. In this case, you can prevent the traffic of one subnet from being routed to another subnet of the same port by configuring the port or trunk as both the source and destination for traffic to drop.
Example:
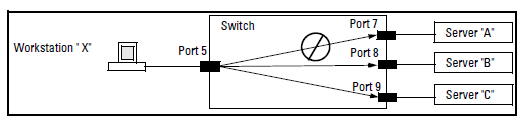
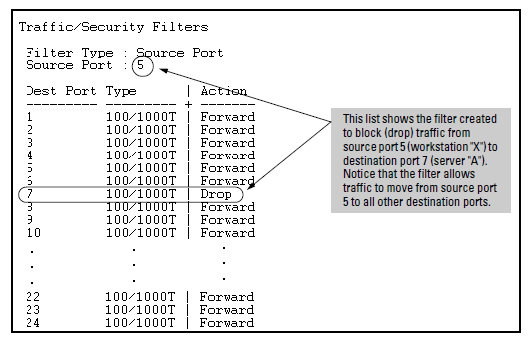
If you wanted to prevent server “A” from receiving traffic sent by workstation “X”, but do not want to prevent any other servers or end nodes from receiving traffic from workstation “X”, you would configure a filter to drop traffic from port 5 to port 7. The resulting filter would drop traffic from port 5 to port 7, but would forward all other traffic from any source port to any destination port. (See Filter blocking traffic only from Port 5 to Server A and Filter for the actions shown in Figure 98.
You can specify named source-port filters that may be used on multiple ports and port trunks. A port or port trunk can only have one source-port filter, but by using this capability you can define a source-port filter once and apply it to multiple ports and port trunks. This can make it easier to configure and manage source-port filters on your switch. The commands to define, configure, apply, and display the status of named source-port filters are described below.
-
A port or port trunk may only have one source-port filter, named or not named.
-
A named source-port filter can be applied to multiple ports or port trunks.
-
Once a named source-port filter is defined, subsequent changes only modify its action, they don’t replace it.
-
To change the named source-port filter used on a port or port trunk, the current filter must first be removed, using the
no filter source-port named-filter <command.filter-name> -
A named source-port filter can only be deleted when it is not applied to any ports.
The named source-port filter command operates from the global configuration level.
Syntax:
Defines or deletes a named source-port filter. The <
> may contain a maximum of 20 alpha-numeric characters (longer names may be specified, but they are not displayed.) A filter-name cannot be a valid port or port trunk name.filter-nameThe maximum number of named source-port filters that can be used is equal to the number of ports on a switch.
A named source-port filter can only be removed if it is not in use (use the
show filter source-portcommand to check the status). Named source-port filters are not automatically deleted when they are no longer used.Use the
nooption to delete an unused named source-port filter.
Syntax:
Configures the named source-port filter to drop traffic having a destination on the ports and/or port trunks in the <
>. Can be followed by thedestination-port-listforwardoption if you have other destination ports or port trunks previously set to drop that you want to change toforward.For example:
filter source-port named-filter <.filter-name> drop <destination-port-list> forward <destination-port-list>The
destination-port-listmay contain ports, port trunks, and ranges (for example 3-7 or trk4-trk9) separated by commas.
Syntax:
Configures the named source-port filter to forward traffic having a destination on the ports and/or port trunks in the
<destination-port-list>. Since “forward” is the default state for destinations in a filter, this command is useful when destinations in an existing filter are configured for “drop” and you want to change them to ”forward”. Can be followed by thedropoption if you have other destination ports set toforwardthat you want to change todrop.For example:
filter source-port named-filter <filter-name> forward <destination-port-list> drop <destination-port-list>
A named source-port filter must first be defined and configured before it can be applied. In the following example two named source-port filters are defined, web-only and accounting.
HP Switch(config)# filter source-port named-filter web-onlyHP Switch(config)# filter source-port named-filter accounting
By default, these two named source-port filters forward traffic to all ports and port trunks.
To configure a named source-port filter to prevent inbound traffic from being forwarded to specific destination switch ports or port trunks, the dropoption is used. For example, on a 26-port switch, to configure the named source-port filter web-only to drop any traffic except that for destination ports 1 and 2, the following command would be used:
A named source-port filter can be defined and configured in a single command by adding the drop option, followed by the required destination-port-list.
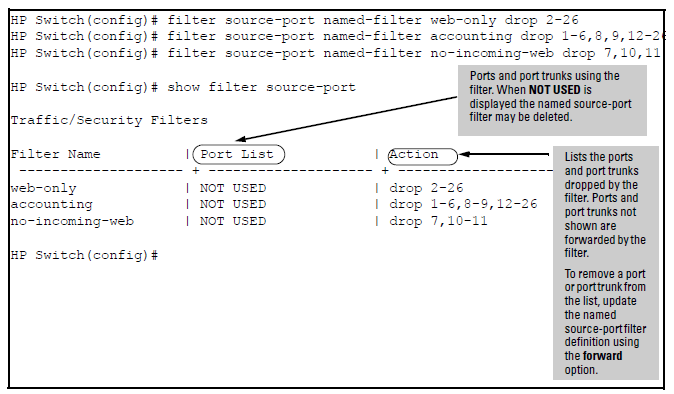
You can list all source-port filters configured in the switch, both named and unnamed, and their action using the show command below.
Syntax:
Displays a listing of configured source-port filters, where each filter entry includes a Filter Name, Port List, and Action:
Filter Name
The filter-name used when a named source-port filter is defined. Non-named source-port filters are automatically assigned the port or port trunk number of the source port.
Port List
Lists the port and port trunk destinations using the filter. Named source-port filters that are not in use display NOT USED.
Action
Lists the ports and port trunks dropped by the filter. If a named source-port filter has been defined but not configured, this field is blank.
[index]
For the supplied index (IDX) displays the action taken (Drop or Forward) for each destination port on the switch.
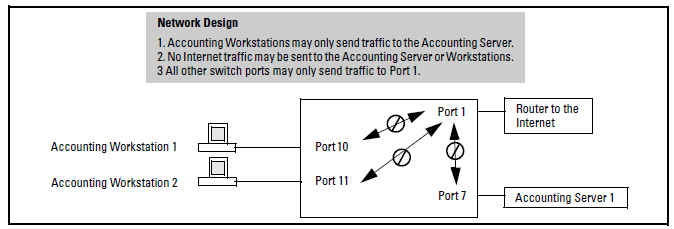
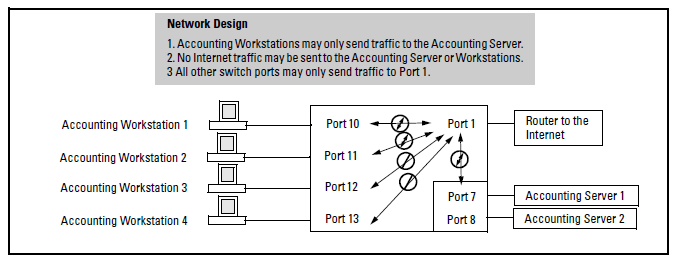
A company wants to manage traffic to the Internet and its accounting server on a 26-port switch. Their network is pictured in Network configuration for named source-port filters. Switch port 1 connects to a router that provides connectivity to a WAN and the Internet. Switch port 7 connects to the accounting server. Two workstations in accounting are connected to switch ports 10 and 11.
Example:
While named source-port filters may be defined and configured in two steps, this is not necessary. Here we define and configure each of the named source-port filters for our example network in a single step.
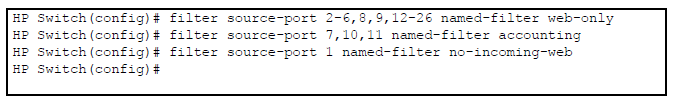
Once the named source-port filters have been defined and configured we now apply them to the switch ports.
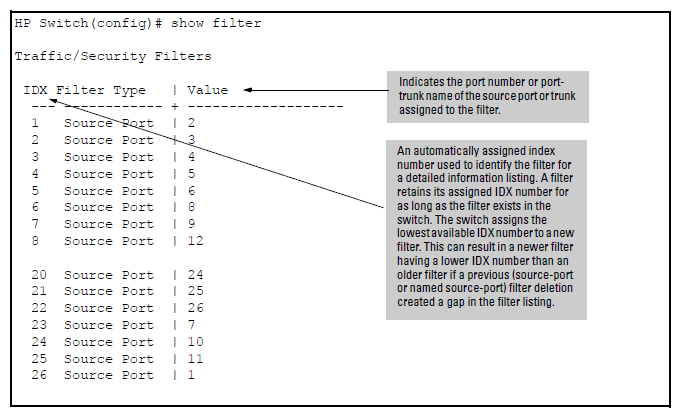
The show filter command shows what ports have filters applied.
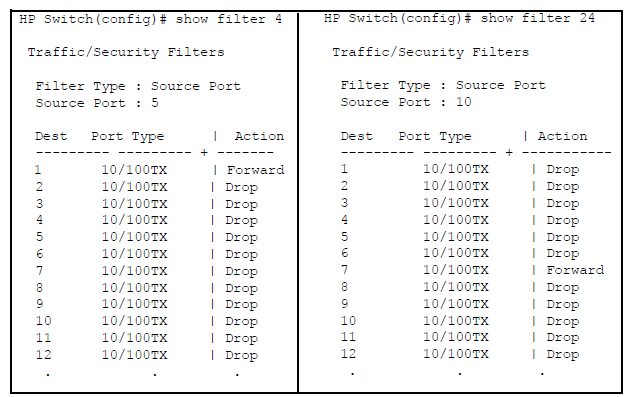
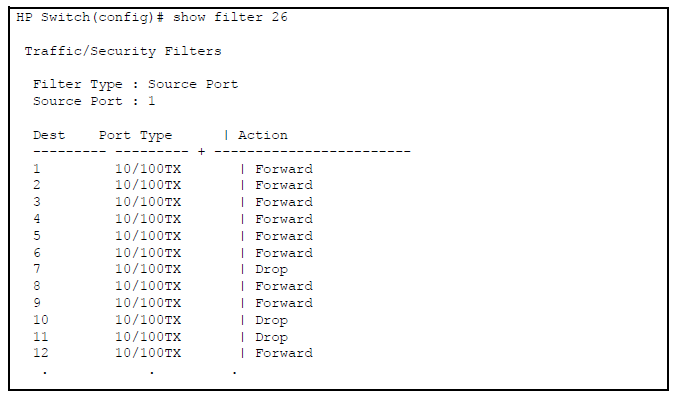
Using the IDX value in the show filter command, we can see how traffic is filtered on a specific port (Value). The two outputs below show a non-accounting and an accounting switch port.
The same command, using IDX 26, shows how traffic from the Internet is handled.
As the company grows, more resources are required in accounting. Two additional accounting workstations are added and attached to ports 12 and 13. A second server is added attached to port8.
The following revisions to the named source-port filter definitions maintain the desired network traffic management, as shown in the Action column of the show command.
Network traffic management with source port filters
HP Switch(config)# filter source-port named-filter accounting forward 8,12,13 HP Switch(config)# filter source-port named-filter no-incoming-web drop 8,12,13 HP Switch(config)# HP Switch(config)# show filter source-port Traffic/Security Filters Filter Name | Port List | Action ------------------ + ----------------- + ---------------- web-only | 2-6,8-9,12-26 | drop 2-26 accounting | 7,10-11 | drop 1-6,9,14-26 no-incoming-web | 1 | drop 7-8,10-13 HP Switch(config)#
We next apply the updated named source-port filters to the appropriate switch ports. As a port can only have one source-port filter (named or not named), before applying the new named source-port filters we first remove the existing source-port filters on the port.
No filter source-port
HP Switch(config)# no filter source-port 8,12,13 HP Switch(config)# filter source-port 8,12,13 named-filter accounting HP Switch(config)#
The named source-port filters now manage traffic on the switch ports as shown below, using the show filter source-port command.
Named source-port filters managing traffic
HP Switch(config)# show filter source-port Traffic/Security Filters Filter Name | Port List | Action ------------------ + ----------------- + ---------------- web-only | 2-6,8-9,14-26 | drop 2-26 accounting | 7-8,10-13 | drop 1-6,9,14-26 no-incoming-web | 1 | drop 7-8,10-13 HP Switch(config)#
This filter type enables the switch to forward or drop multicast traffic to a specific set of destination ports. This helps to preserve bandwidth by reducing multicast traffic on ports where it is unnecessary, and to isolate multicast traffic to enhance security.
You can configure up to 16 static multicast filters (defined by the filter command). However, if an IGMP-controlled filter for a joined multicast group has the same multicast address as a static multicast filter configured on a given port, the IGMP-controlled filter overrides the static multicast filter configured on that port. Note that in the default configuration, IGMP is disabled on VLANs configured in the switch. To enable IGMP on a specific VLAN, use the vlan < command. (For more on this command, see “Multimedia Traffic Control with IP Multicast (IGMP)” in the Multicast and Routing Guide for your switch.)vid> ip igmp
The total of static multicast filters and IGMP multicast filters together can range from 389 to 420, depending on the current max-vlans setting in the switch. If multiple VLANs are configured, then each filter is counted once per VLAN in which it is used.
Multicast filer limits
| Max-VLANs setting | Max # multicast filters (static and IGMP combined) |
|---|---|
| 1 (minimum) | 420 |
| 8 (default) | 413 |
| 32 or higher | 389 |
|
|
|
![[CAUTION: ]](images/caution.gif) |
CAUTION: If Spanning Tree is enabled, then the MSTP multicast MAC address (0180c2- 000000) should not be filtered. (STP will not operate properly if the MSTP multicast MAC address is filtered.) |
|
|
This filter type enables the switch to forward or drop, on the basis of protocol type, traffic to a specific set of destination ports on the switch. Filtered protocol types include:
| Appletalk | NetBEUI |
| ARP | SNA |
| IPX |
Only one filter for a particular protocol type can be configured at any one time. For example, a separate protocol filter can be configured for each of the protocol types listed above, but only one of those can be an IP filter. Also, the destination ports for a protocol filter can be on different VLANs.