ARP restricted forwarding configuration example
Network requirements
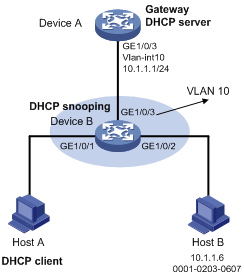
As shown in Figure 139, configure ARP restricted forwarding on Device B where ARP attack detection is configured. Port isolation configured on Device B can take effect for broadcast ARP requests.
Figure 138: Network diagram
Configuration procedure
Configure VLAN 10, add interfaces to VLAN 10, and specify the IP address of VLAN-interface 10 on Device A. (Details not shown.)
Configure the DHCP server on Device A, and configure DHCP address pool 0.
<DeviceA> system-view [DeviceA] dhcp enable [DeviceA] dhcp server ip-pool 0 [DeviceA-dhcp-pool-0] network 10.1.1.0 mask 255.255.255.0
Configure Host A (DHCP client) and Host B. (Details not shown.)
Configure Device B:
# Enable DHCP snooping, and configure GigabitEthernet 1/0/3 as a DHCP trusted interface.
<DeviceB> system-view [DeviceB] dhcp snooping enable [DeviceB] interface gigabitethernet 1/0/3 [DeviceB-GigabitEthernet1/0/3] dhcp snooping trust [DeviceB-GigabitEthernet1/0/3] quit
# Enable ARP attack detection for user validity check.
[DeviceB] vlan 10 [DeviceB-vlan10] arp detection enable
# Configure GigabitEthernet 1/0/3 as an ARP trusted interface.
[DeviceB-vlan10] interface gigabitethernet 1/0/3 [DeviceB-GigabitEthernet1/0/3] arp detection trust [DeviceB-GigabitEthernet1/0/3] quit
# Configure a static IP source guard entry on interface GigabitEthernet 1/0/2.
[DeviceB] interface gigabitethernet 1/0/2 [DeviceB-GigabitEthernet1/0/2] ip source binding ip-address 10.1.1.6 mac-address 0001-0203-0607 vlan 10 [DeviceB-GigabitEthernet1/0/2] quit
# Enable ARP packet validity check by checking the MAC addresses and IP addresses of ARP packets.
[DeviceB] arp detection validate dst-mac ip src-mac
# Configure port isolation.
[DeviceB] port-isolate group 1 [DeviceB] interface gigabitethernet 1/0/1 [DeviceB-GigabitEthernet1/0/1] port-isolate enable group 1 [DeviceB-GigabitEthernet1/0/1] quit [DeviceB] interface gigabitethernet 1/0/2 [DeviceB-GigabitEthernet1/0/2] port-isolate enable group 1 [DeviceB-GigabitEthernet1/0/2] quit
After the configurations are completed, Device B first checks the validity of ARP packets received on GigabitEthernet 1/0/1 and GigabitEthernet 1/0/2. If the ARP packets are confirmed valid, Device B performs user validity check by using the static IP source guard bindings and finally DHCP snooping entries. However, ARP broadcast requests sent from Host A can pass the check on Device B and reach Host B. Port isolation fails.
# Enable ARP restricted forwarding.
[DeviceB] vlan 10 [DeviceB-vlan10] arp restricted-forwarding enable [DeviceB-vlan10] quit
After the configuration is completed, Device B forwards ARP broadcast requests from Host A to Device A through the trusted interface GigabitEthernet 1/0/3. Host B cannot receive such packets. Port isolation operates correctly.