Configuration example
Network requirements
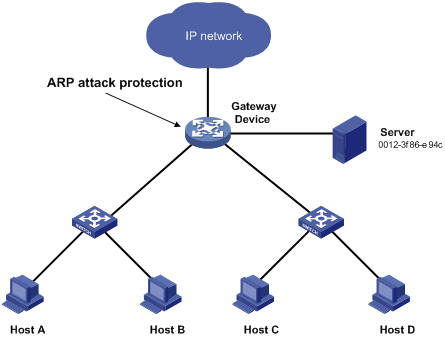
As shown in Figure 135, the hosts access the Internet through a gateway (Device). If malicious users send a large number of ARP requests to the gateway, the gateway might crash and cannot process requests from the clients. To solve this problem, configure source MAC-based ARP attack detection on the gateway.
Figure 134: Network diagram
Configuration considerations
An attacker might forge a large number of ARP packets by using the MAC address of a valid host as the source MAC address. To prevent such attacks, configure the gateway in the following steps:
Enable source MAC-based ARP attack detection and specify the handling method as filter.
Set the threshold.
Set the lifetime for ARP attack entries.
Exclude the MAC address of the server from this detection.
Configuration procedure
# Enable source MAC-based ARP attack detection, and specify the handling method as filter.
<Device> system-view [Device] arp source-mac filter
# Set the threshold to 30.
[Device] arp source-mac threshold 30
# Set the lifetime for ARP attack entries to 60 seconds.
[Device] arp source-mac aging-time 60
# Exclude MAC address 0012-3f86-e94c from this detection.
[Device] arp source-mac exclude-mac 0012-3f86-e94c