Publickey authentication enabled SFTP client configuration example
Network requirements
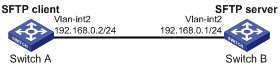
As shown in Figure 116, Switch B acts as the SFTP server, and it uses publickey authentication and the RSA public key algorithm.
Establish an SFTP connection between Switch A and Switch B, so that you can log in to Switch B to manage and transfer files.
Figure 115: Network diagram
Configuration procedure
In the server configuration, the client's host public key is required. Generate RSA key pairs on the client before configuring the SFTP server.
Configure the SFTP client:
# Assign an IP address to VLAN-interface 2.
<SwitchA> system-view [SwitchA] interface vlan-interface 2 [SwitchA-Vlan-interface2] ip address 192.168.0.2 255.255.255.0 [SwitchA-Vlan-interface2] quit
# Generate RSA key pairs.
[SwitchA] public-key local create rsa The range of public key size is (512 ~ 2048). If the key modulus is greater than 512, it will take a few minutes. Press CTRL+C to abort. Input the modulus length [default = 1024]: Generating Keys... ........................++++++ ...................++++++ ..++++++++ ............++++++++ Create the key pair successfully.
# Export the host public key to a public key file named pubkey.
[SwitchA] public-key local export rsa ssh2 pubkey [SwitchA] quit
# Transmit the public key file pubkey to the server through FTP or TFTP. (Details not shown.)
Configure the SFTP server:
# Generate RSA key pairs.
<SwitchB> system-view [SwitchB] public-key local create rsa The range of public key size is (512 ~ 2048). If the key modulus is greater than 512, it will take a few minutes. Press CTRL+C to abort. Input the modulus length [default = 1024]: Generating Keys... ........................++++++ ...................++++++ ..++++++++ ............++++++++ Create the key pair successfully.
# Generate a DSA key pair.
[SwitchB] public-key local create dsa The range of public key size is (512 ~ 2048). If the key modulus is greater than 512, it will take a few minutes. Press CTRL+C to abort. Input the modulus length [default = 1024]: Generating Keys... .++++++++++++++++++++++++++++++++++++++++++++++++++* ........+......+.....+......................................+ ...+.................+..........+...+ Create the key pair successfully.
# Generate an ECDSA key pair.
[SwitchB] public-key local create ecdsa secp256r1 Generating Keys... . Create the key pair successfully.
# Enable the SFTP server.
[SwitchB] sftp server enable
# Assign an IP address to VLAN-interface 2. The SSH client uses this address as the destination for SSH connection.
[SwitchB] interface vlan-interface 2 [SwitchB-Vlan-interface2] ip address 192.168.0.1 255.255.255.0 [SwitchB-Vlan-interface2] quit
# Import the peer public key from the public key file pubkey, and name it switchkey.
[SwitchB] public-key peer switchkey import sshkey pubkey
# Create an SSH user named client001. Specify the service type as sftp and the authentication method as publickey for the user. Assign the public key switchkey to the user.
[SwitchB] ssh user client001 service-type sftp authentication-type publickey assign publickey switchkey
# Create a local device management user named client001.
[SwitchB] local-user client001 class manage
# Authorize local user client001 to use the SSH service.
[SwitchB-luser-manage-client001] service-type ssh
# Assign the network-admin user role and working directory flash:/ to local user client001.
[SwitchB-luser-manage-client001] authorization-attribute user-role network-admin work-directory flash:/ [SwitchB-luser-manage-client001] quit
Establish a connection to the SFTP server:
# Establish a connection to the SFTP server and enter SFTP client view.
<SwitchA> sftp 192.168.0.1 identity-key rsa Username: client001 Press CTRL+C to abort. Connecting to 192.168.0.1 port 22. The server is not authenticated. Continue? [Y/N]:y Do you want to save the server public key? [Y/N]:n sftp>
# Display files under the current directory of the server, delete file z, and verify the result.
sftp> dir -l -rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg -rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2 -rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new -rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub -rwxrwxrwx 1 noone nogroup 0 Sep 01 08:00 z sftp> delete z Removing /z sftp> dir -l -rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg -rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2 -rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new -rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
# Add a directory named new1 and verify the result.
sftp> mkdir new1 sftp> dir -l -rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg -rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2 -rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new -rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub drwxrwxrwx 1 noone nogroup 0 Sep 02 06:30 new1
# Change the name of directory new1 to new2 and verify the result.
sftp> rename new1 new2 sftp> dir -l -rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg -rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2 -rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new -rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
# Download file pubkey2 from the server and save it as a local file named public.
sftp> get pubkey2 public Fetching / pubkey2 to public /pubkey2 100% 225 1.4KB/s 00:00
# Upload the local file pu to the server, save it as puk, and verify the result.
sftp> put pu puk Uploading pu to / puk sftp> dir -l -rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg -rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2 -rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2 -rwxrwxrwx 1 noone nogroup 283 Sep 02 06:35 pub -rwxrwxrwx 1 noone nogroup 283 Sep 02 06:36 puk sftp>
# Exit SFTP client view.
sftp> quit <SwitchA>