ASPF inspections
This section introduces the basic idea of ASPF inspection on application layer and transport layer protocols.
Application layer protocol inspection
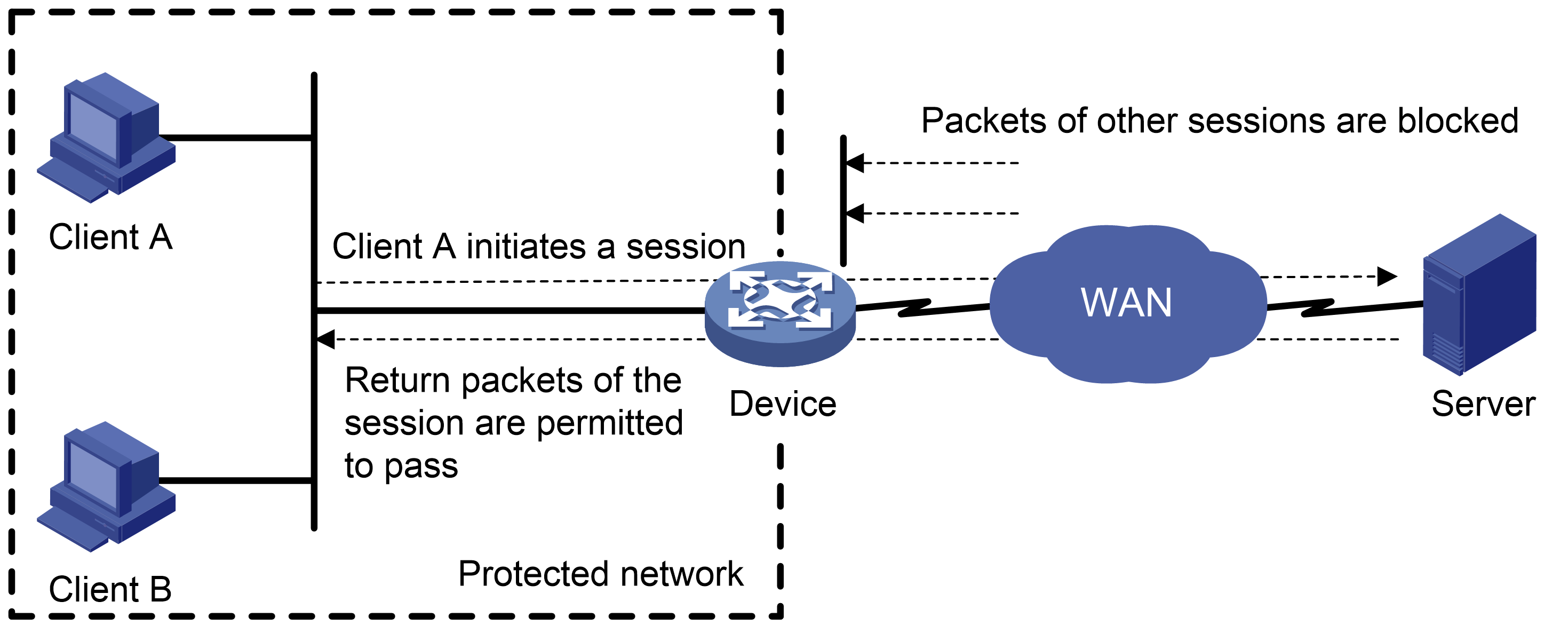
As shown in Figure 171, ACLs on the edge device deny incoming packets to the internal network. The ASPF application layer protocol inspection allows return packets from the external network to the internal network.
Figure 166: Application layer protocol inspection
ASPF inspects all application layer sessions as follows:
For a single-channel protocol, the inspection process is simple.
ASPF creates a session entry immediately after it detects the session's first packet sent to the external network, and ASPF removes the entry when the connection is terminated.
The session entry helps record outgoing packets and their return packets. It can maintain the session status and determine whether state transitions of the session are correct. All packets that match a session entry can pass through the packet-filter firewall.
For a multichannel protocol, ASPF creates session entries, and one or more associated entries to associate the sessions initiated by the same application layer protocol. Associated entries are created during the protocol negotiation and are removed after the negotiation. ASPF uses the associated entries to match the first packets of the sessions. All packets of the sessions matching the associated entries can pass through the packet-filter firewall.
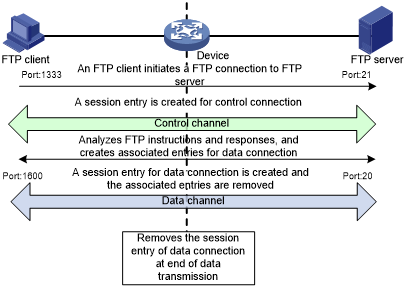
The following uses FTP to explain the process of multichannel application layer protocol inspection.
Figure 167: FTP inspection
As shown in Figure 172, FTP connections are established and removed as follows:
The FTP client initiates an FTP control connection from port 1333 to port 21 of the FTP server.
As a result of negotiation, the server initiates a data connection from port 20 to port 1600 of the client.
When data transmission times out or ends, the data connection is removed.
ASPF implements FTP inspection during the FTP connection lifetime as follows:
ASPF checks the IP packets the FTP client sends to the FTP server to identify TCP-based FTP packets. Based on the port number, ASPF identifies the control connection between the FTP client and server and creates a control connection session entry.
ASPF checks each FTP control connection packet, and examines their TCP status based on the control connection session entry. ASPF analyzes the FTP instructions in the control connection packet. If the packet contains a data channel setup instruction, ASPF creates an associated entry for the data connection.
For return FTP control connection packets, ASPF examines their TCP status based on the control connection session entry to make packet forwarding decisions.
When the FTP data passes through the device, ASPF is triggered to create a session entry for the data connection and remove the associated entry.
For returned FTP data packets, ASPF examines their TCP status based on the data connection session entry to make packet forwarding decisions.
When the data transmission ends, ASPF removes the data connection session entry. When the FTP connection is removed, ASPF removes the control connection session entry.
Transport layer protocol inspection
The transport layer protocol inspection refers to generic TCP/UDP inspection. It creates session entries to record the transport layer information of the packets to dynamically filter TCP and UDP packets. The transport layer information includes source and destination addresses and port numbers.
Generic TCP/UDP inspection requires that return packets must match the corresponding packets that are previously sent out of the external interface. The return packets must have the same source/destination addresses and source/destination port numbers as the outgoing packets (but reversed). Otherwise, the return packets are blocked. For multichannel application layer protocols like FTP, the deployment of TCP inspection without application layer inspection leads to failure of establishing a data connection.