IKE remote extended authentication configuration example
Network requirements
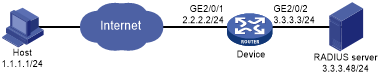
As shown in Figure 144, configure an IPsec tunnel to protect the traffic between the host and the device.
Set up IPsec SAs through IKE negotiations.
Configure the host and the device to use pre-shared key for authentication in the phase-1 IKE negotiation.
Configure the device to use RADIUS to perform remote extended authentication on the host.
Figure 139: Network diagram
Configuration procedure
Before you configure the device, perform the following tasks:
Make sure the host and the device can reach each other.
Configure the RADIUS server. Make sure the RADIUS server has an authentication account for the host. In this example, the account uses username test and password abc.
Configure the device:
# Configure IP addresses for interfaces. (Details not shown.)
# Create a RADIUS scheme named ike-scheme.
[Device] radius scheme ike-scheme
# Specify the IP address and service port of the primary RADIUS authentication server.
[Device-radius-ike-scheme] primary authentication 3.3.3.48 1645
# Set the shared key for secure RADIUS authentication communication.
[Device-radius-ike-scheme] key authentication simple abc
# Configure the device to send the username without the ISP domain name to the RADIUS server. (The configuration varies with the RADIUS server's requirements for username.)
[Device-radius-ike-scheme] user-name-format without-domain [Device-radius-ike-scheme] quit
# Create an ISP domain named ike and specify the RADIUS scheme used for authenticating the IKE users.
[Device] domain ike [Device-isp-ike] authentication ike radius-scheme ike-scheme [Device-isp-ike] quit
# Configure an IPv4 advanced ACL to identify the packets to be protected.
[Device] acl advanced 3101 [Device-acl-ipv4-adv-3101] rule permit ip source 2.2.2.2 0.0.0.0 destination 1.1.1.1 0.0.0.0 [Device-acl-ipv4-adv-3101] quit
# Created an IPsec transform set named tran1.
[Device] ipsec transform-set tran1
# Specify the encapsulation mode as transport.
[Device-ipsec-transform-set-tran1] encapsulation-mode transport
# Specify the security protocol as ESP.
[Device-ipsec-transform-set-tran1] protocol esp
# Specify the ESP authentication algorithm and encryption algorithm.
[Device-ipsec-transform-set-tran1] esp encryption-algorithm aes-cbc-128 [Device-ipsec-transform-set-tran1] esp authentication-algorithm sha1 [Device-ipsec-transform-set-tran1] quit
# Create an IKE keychain named keychain1.
[Device] ike keychain keychain1
# Set the pre-shared key used for IKE negotiation with the peer 1.1.1.1.
[Device-ike-keychain-keychain1] pre-shared-key address 1.1.1.1 255.255.255.255 key simple 123456TESTplat&! [Device-ike-keychain-keychain1] quit
# Create an IKE profile named profile1.
[Device] ike profile profile1
# Specify the IKE keychain for the IKE profile.
[Device-ike-profile-profile1] keychain keychain1
# Configure the local ID as the IP address 2.2.2.2.
[Device-ike-profile-profile1] local-identity address 2.2.2.2
# Configure the peer ID for IKE profile matching.
[Device-ike-profile-profile1] match remote identity address 1.1.1.1 255.255.255.255 [Device-ike-profile-profile1] quit
# Enable XAUTH authentication for clients.
[Device-ike-profile-profile1] client-authentication xauth [Device-ike-profile-profile1] quit
# Create an IKE-based IPsec policy entry. Specify the policy name as map1 and set the sequence number to 10.
[Device] ipsec policy map1 10 isakmp
# Specify the remote IP address for the IPsec tunnel.
[Device-ipsec-policy-isakmp-map1-10] remote-address 1.1.1.1
# Specify the ACL.
[Device-ipsec-policy-isakmp-map1-10] security acl 3101
# Specify the IPsec transform set.
[Device-ipsec-policy-isakmp-map1-10] transform-set tran1
# Specify the IKE profile.
[Device-ipsec-policy-isakmp-map1-10] ike-profile profile1 [Device-ipsec-policy-isakmp-map1-10] quit
# Apply the IPsec policy to GigabitEthernet 2/0/1.
[Device] interface gigabitethernet 2/0/1 [Device-GigabitEthernet2/0/1] ipsec apply policy map1 [Device-GigabitEthernet2/0/1] quit
Configure the host:
Perform the following tasks on the host and make sure the configuration matches that on the device:
Specify the IP address of the remote security gateway.
Set the pre-shared key used for IKE negotiation.
Configure the username and password for IKE extended authentication.
Specify the security protocol, encryption algorithm, and authentication algorithm.
Configure IKE negotiation parameters.
Configure the local ID and remote ID.
(Details not shown.)
Verifying the configuration
# Initiate a connection from the host (1.1.1.1) to the device (2.2.2.2) to trigger IKE negotiation. (Details not shown.)
# On the device, verify that an IKE SA to the peer 1.1.1.1 is established and extended authentication is enabled for remote users.
[Device] display ike sa verbose remote-address 1.1.1.1 ----------------------------------------------- Connection ID: 18 Outside VPN: Inside VPN: Profile: profile1 Transmitting entity: Initiator ----------------------------------------------- Local IP: 2.2.2.2 Local ID type: IPV4_ADDR Local ID: 2.2.2.2 Remote IP: 1.1.1.1 Remote ID type: IPV4_ADDR Remote ID: 1.1.1.1 Authentication-method: PRE-SHARED-KEY Authentication-algorithm: SHA1 Encryption-algorithm: DES-CBC Life duration(sec): 86400 Remaining key duration(sec): 84565 Exchange-mode: Aggressive Diffie-Hellman group: Group 1 NAT traversal: Detected Extend authentication: Enabled Assigned IP address:
# On the host, enter the correct username and password for extended authentication. After the authentication succeeds, the IPsec tunnel will be established. (Details not shown.)
# Verify that IPsec SAs have been established on the device.
[Device] display ipsec sa