Configuring per-port filtering
Syntax
filter connection-rate < port-list > < notify-only | throttle | block >
no filter connection-rate < port-list >
Configures the per-port policy for responding to detection of a relatively high number of inbound IP connection attempts from a given source. The level at which the switch detects such traffic depends on the sensitivity setting configured by the
connection-rate-filter sensitivity command.
You can use connection-rate ACLs to create exceptions to the configured filtering policy.
The
no form of the command disables connection-rate filtering on the ports in #
<port-list>.
The
notify-onlyoption can be used if the switch detects a relatively high number of IP connection attempts from a specific host,
notify-only generates an Event Log message and sends a similar message to any SNMP trap receivers configured on the switch.
The
throttle command can be used if the switch detects a relatively high number of IP connection attempts from a specific host, this option generates the
notify-only messaging and blocks all inbound traffic from the offending host for a penalty period. After the penalty period, the switch allows traffic from the offending host to resume, and re-examines the traffic. If the suspect behavior continues, the switch again blocks the traffic from the offending host and repeats the cycle. For the penalty periods, see
Table 7: Throttle mode penalty periodsShow CLIsTroubleshootingConfiguration commandsShow commandSecure Radius (RadSec).
The
block command can be used if the switch detects a relatively high number of IP connection attempts from a specific host, this option generates the
notify-only messaging and also blocks all inbound traffic from the offending host.
Throttle mode (sensitivity) |
Frequency of IP connection requests from the same source |
Mean number of new destination hosts in the frequency period |
Penalty period |
|---|---|---|---|
Low |
<0.1 second |
54 |
<30 seconds |
Medium |
<1.0 second |
37 |
30 - 60 seconds |
High |
<1.0 second |
22 |
60 - 90 seconds |
Aggressive |
<1.0 second |
15 |
90 - 120 seconds |
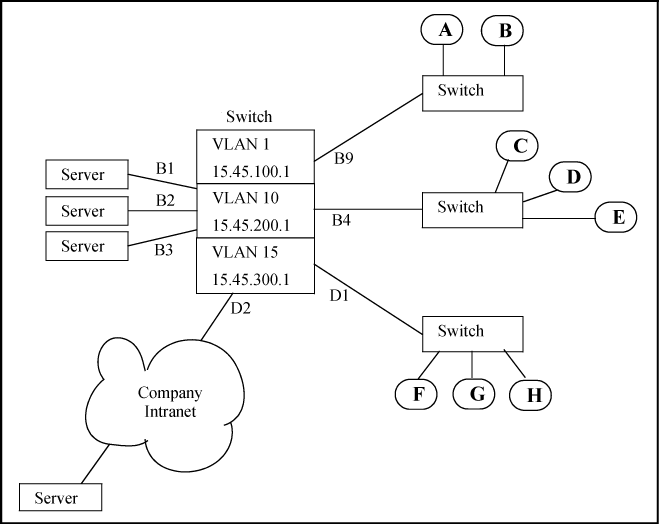
Example of a Basic Connection-Rate Filtering Configuration