Example of RadSec configuration
Prerequisite
ClearPass version is 6.7.4 or higher.
ClearPass as RadSec server
Following are the steps to configure ClearPass as RadSec server:
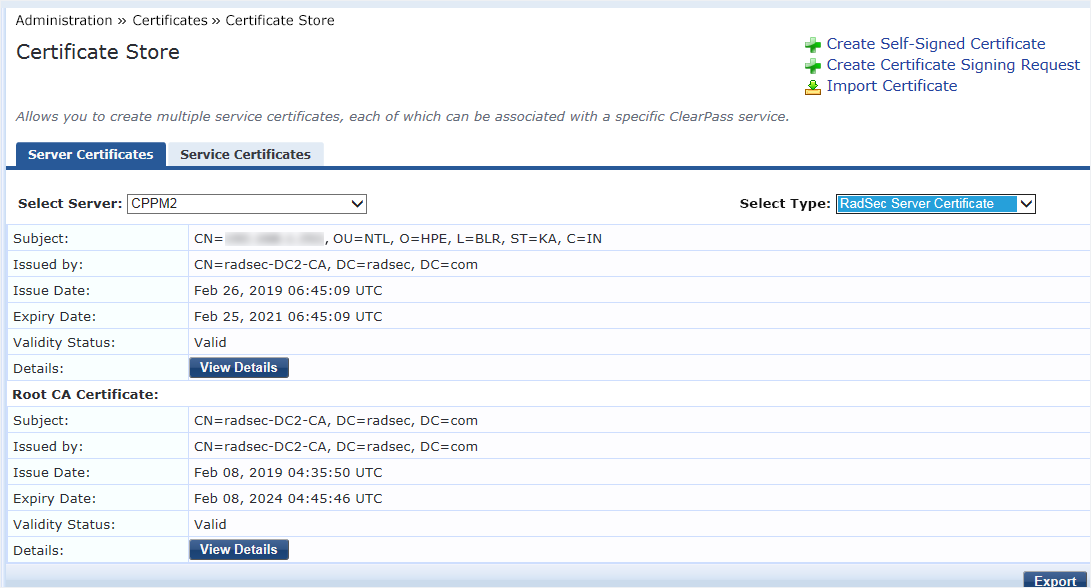
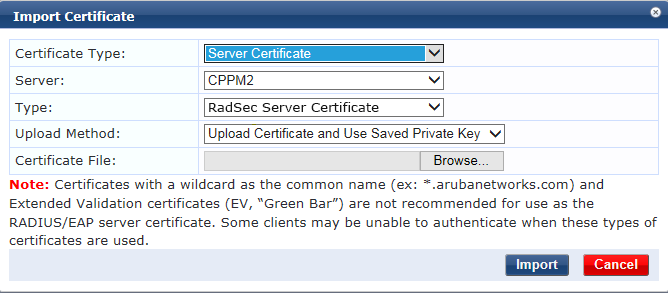
Import Root CA certificate to the ClearPass certificate store. Choose Select Type as RadSec Server Certificate
Click Create Certificate Signing Request.
Enter the IP address of ClearPass . For configuring radius-server host FQDN on DUT, enter the hostname.
Sign the created CSR with CA.
Ensure RadSec Server Certificate is selected while importing signed certificate.
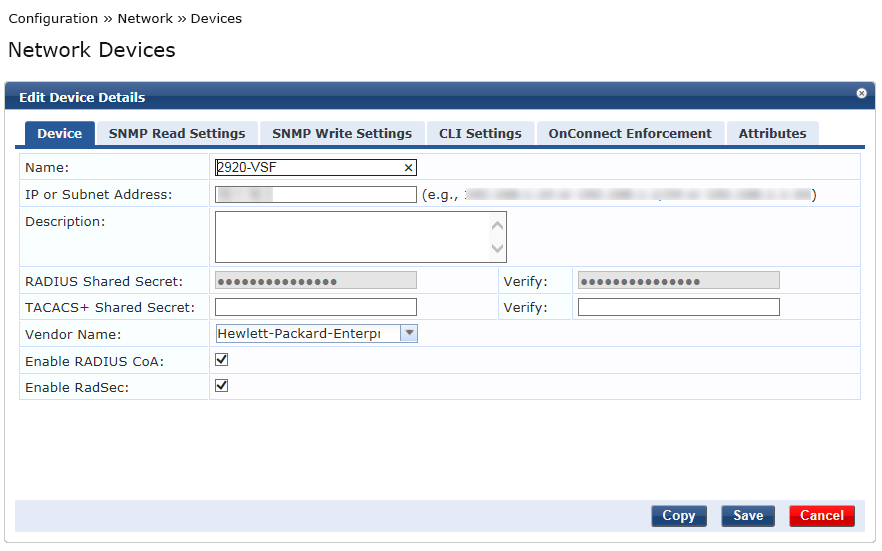
Select Enable RadSec while adding devices.
The IP address is used as the source IP of the DUT and must be reachable from ClearPass.
DUT configuration
Follow these steps to configure DUT:
- Generate CSR with usage
radsec-clientDUT(config)# crypto pki ta-profile ta1 DUT(config)# crypto pki create-csr certificate-name Cert1 ta-profile ta1 key-type rsa key-size 2048 subject common-name test org HEP org-unit HPN state KA country IN usage radsec-client Copy CA root certificate generated on CA.
DUT(config)# copy tftp ta-certificate ta1 <tftp server ip> certnew.cer- Sign the CSR with CA.
- Install the signed certificate.
DUT(config)# crypto pki install-signed-certificate Verify the installed Root and Local certificate.
DUT(config)# sh crypto pki ta-profile Profile Name Profile Status CRL Configured OCSP Configured --------------- ------------------------------ --------------- --------------- IDEVID_ROOT Root Certificate Installed COMODO_CA Root Certificate Installed No No default Self-signed Certificate Ins... No No GEOTRUST_CA Root Certificate Installed No No ARUBA_CA Root Certificate Installed No No ADDTRUST_CA Root Certificate Installed No No clearpass Root Certificate Installed No No ta1 Root Certificate Installed No No DUT(config)# sh crypto pki local-certificate Name Usage Expiration Parent / Profile -------------------- ------------- -------------- -------------------- IDEVID_CERT IDEVID 2031/01/26 IDEVID_INTER_1 IDEVID_INTER_1 IDEVID 2031/01/26 IDEVID_INTER_2 IDEVID_INTER_2 IDEVID 2031/01/26 IDEVID_ROOT test All 2019/08/13 default Test_Certificate Web 2019/08/03 default Cert1 RADSEC 2020/02/14 ta1 DUT(config)#- Configure radius-server with
tlsoption.DUT(config)# radius-server host 192.168.1.252 tls Enable debug commands.
Debug security RadSec Debug security radiusVerify the RadSec connection.
DUT(config)# show radius host 192.168.1.252 Status and Counters - RADIUS Server Information Server IP Addr : 192.168.1.252 TLS Enabled : Yes Authentication Port : 2083 Accounting Port : 2083 Round Trip Time : 4 Round Trip Time : 0 Pending Requests : 0 Pending Requests : 0 Retransmissions : 0 Retransmissions : 0 Timeouts : 78 Timeouts : 0 Malformed Responses : 0 Malformed Responses : 0 Bad Authenticators : 2 Bad Authenticators : 0 Unknown Types : 0 Unknown Types : 0 Packets Dropped : 10 Packets Dropped : 0 Access Requests : 1435 Accounting Requests : 0 Access Challenges : 22 Accounting Responses : 0 Access Accepts : 11 Access Rejects : 1324 Connection Status : RADSEC Connection established Connection Error : NA