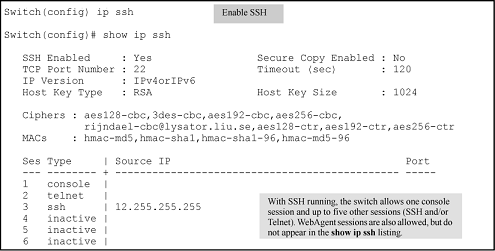
Enabling SSH on the switch and anticipating SSH client contact behavior
When configured for SSH, the switch uses its host public key to authenticate itself to SSH clients. For SSH clients to authenticate themselves to the switch, configure SSH on the switch for client public-key authentication at the login (operator) level. To enhance security also configure local, TACACS+, or RADIUS authentication at the enable (manager) level.
See Configuring the switch for SSH authentication and SSH client contact behavior.
The public/private key pair for switch must have been generated. See Generating or erasing the switch public/private host key pair.
ip ssh command.
For the complete syntax, see ip ssh .
Protect your private key file from access by anyone other than yourself. If someone can access your private key file, they can penetrate SSH security on the switch by appearing to be you.
SSH does not protect the switch from unauthorized access via the WebAgent, Telnet, SNMP, or the serial port. While WebAgent and Telnet access can be restricted by the use of passwords local to the switch, if you are unsure of the security this provides, you may want to disable web-based and/or Telnet access (no web-management and
no Telnet). If you need to increase SNMP security, use SNMP version 3 only. To increase the security of your web interface see the section on SSL. For an additional security measure, see the authorized IP managers feature in the
management and configuration guide for your switch. To protect against unauthorized access to the serial port (and the
Clear button, which removes local password protection), keep physical access to the switch restricted to authorized personnel.