Using the standard attribute in an IPv4 ACL (example)
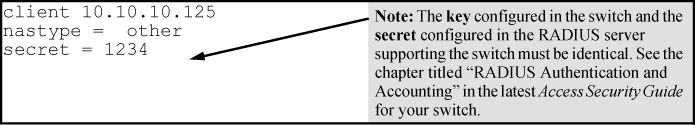
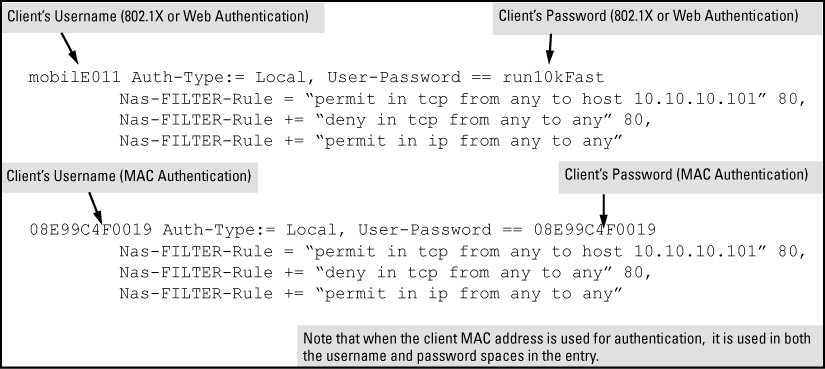
The Standard attribute (92), when used in an ACL without the HP-Nas-Rules-IPv6 VSA, filters IPv4 traffic inbound from the authenticated client. (Any IPv6 traffic inbound from the client is dropped.) This example illustrates configuring RADIUS-assigned IPv4 ACL support on FreeRADIUS using the standard attribute for two different client identification methods (username/password and MAC address).
Procedure