Using an ACL in a connection-rate configuration example
This example adds connection-rate ACLs to the example in Viewing the connection-rate configuration .
-
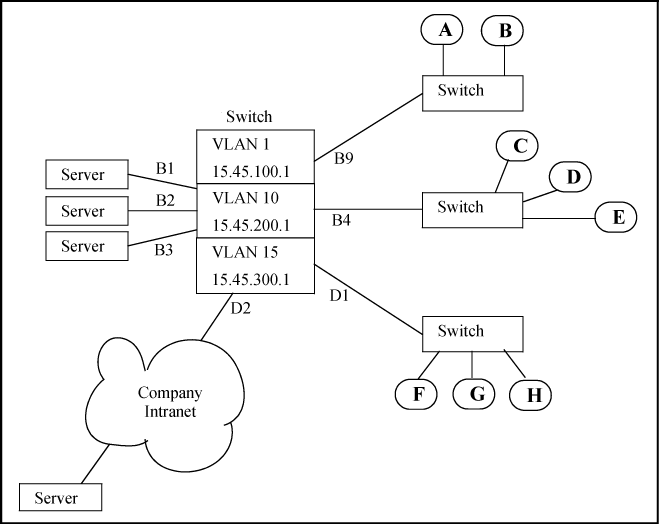
The administrator has elevated the connection-rate sensitivity to
high. -
The server at IP address 15.45.50.17 frequently transmits a relatively high rate of legitimate connection requests, which now triggers connection-rate blocking of the server's IP address on port D2. This causes periodic, unnecessary blocking of access to the server.
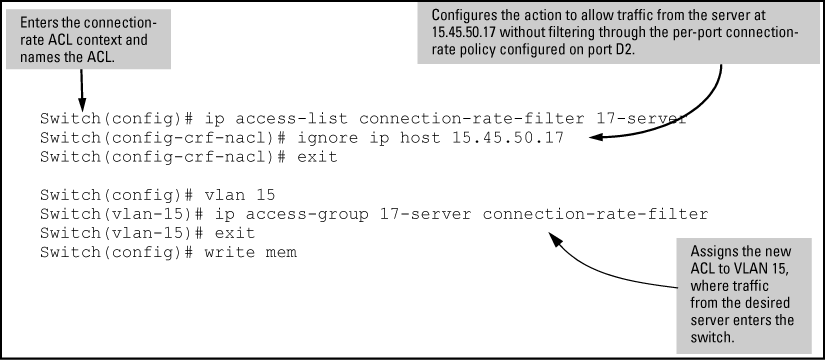
The administrator needs to maintain blocking protection from the "Company Intranet" while allowing access to the server at 15.45.50.17. Because the server is carefully maintained as a trusted device, the administrator's solution is to configure a connection-rate ACL that causes the switch to ignore (circumvent) connection-rate filtering for inbound traffic from the server, while maintaining the filtering for all other inbound traffic on port D2.
The configuration steps include: